The phrase “Bclub Trusted CVV2 Marketplace – High Grade Dumps Available” reflects the type of marketing language commonly used in underground cybercrime forums. These platforms present themselves as bclub organized, reliable, and professional marketplaces for stolen financial data. While the wording may sound legitimate, the reality behind such claims is deeply tied to financial fraud, identity theft, and serious legal consequences.
In today’s digital economy, payment card security is more important than ever. As online transactions grow, so does the risk of data breaches and financial exploitation. Understanding how so-called “trusted” CVV2 marketplaces operate is essential for individuals, businesses, and cybersecurity professionals seeking to defend against fraud.
What Is CVV2 and Why Is It Targeted?
CVV2 stands for Card Verification Value 2. It is the three-digit (or sometimes four-digit) security code printed on a payment card. This code is used primarily for card-not-present transactions, such as online purchases.
Criminals target CVV2 data because:
- It enables unauthorized online transactions
- It bypasses certain basic fraud checks
- It can be combined with stolen card numbers for full access
- It increases the success rate of fraudulent purchases
When combined with cardholder names, expiration dates, and billing details, CVV2 data becomes a powerful tool for fraudsters.
What Are “Dumps”?
“Dumps” refer to data extracted from a card’s magnetic stripe. This information can be used to clone physical cards for in-person transactions.
Data is typically stolen through:
- Point-of-sale malware
- Card skimming devices
- Large-scale data breaches
- Phishing campaigns
- Compromised online databases
Once collected, this information is often sold on hidden marketplaces that advertise “high grade” or “premium” data.
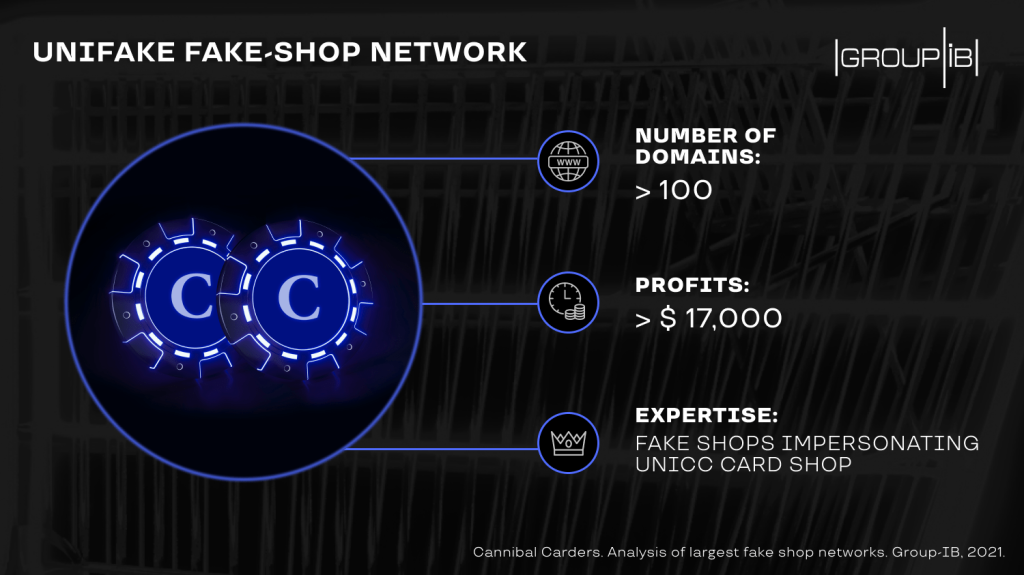
How Underground Marketplaces Build False Trust
Platforms using phrases like “Trusted CVV2 Marketplace” attempt to establish credibility among criminal buyers. They may claim:
- Verified sellers
- Quality-checked data
- Refund policies
- Freshly obtained records
- High approval rates
These tactics mirror legitimate e-commerce strategies. However, there is no real consumer protection in illegal markets. Buyers often face:
- Exit scams
- Law enforcement infiltration
- Malware disguised as downloads
- Cryptocurrency theft
- Account shutdowns
Trust in criminal ecosystems is fragile and temporary. Many participants lose money to scams within the same networks they rely on.
Legal Consequences of Participation
Engaging in buying, selling, or even possessing stolen financial data is a serious crime in most countries. Laws addressing such activities include:
- Identity theft statutes
- Fraud and financial crime regulations
- Computer misuse laws
- Cybercrime enforcement acts
Penalties can include:
- Significant fines
- Asset forfeiture
- Long-term imprisonment
- Permanent criminal records
International cooperation between law enforcement agencies has increased dramatically. Cybercrime investigations now use advanced tools such as blockchain analysis, server tracking, undercover bclub.tk operations, and digital forensics.
The assumption of anonymity in underground markets is often incorrect. Digital footprints are difficult to erase completely.
The Human Cost of Stolen Card Data
Behind every stolen card record is a real person.
Victims of card fraud may experience:
- Unauthorized withdrawals
- Declined legitimate transactions
- Emotional distress
- Credit score damage
- Time spent resolving disputes
While banks often reimburse fraudulent charges, the stress and inconvenience can be significant.
Businesses also suffer. Data breaches lead to:
- Reputational damage
- Regulatory penalties
- Customer trust erosion
- Expensive investigations
- Increased security costs
The broader economy absorbs these losses through higher fees and stricter verification systems.
Why Do These Markets Continue to Operate?
Despite enforcement efforts, underground carding platforms persist due to profitability and demand. Several factors contribute to their survival:
- Growing volume of online transactions
- Weak cybersecurity practices in some organizations
- Successful phishing techniques
- Social engineering vulnerabilities
- Poor password management
Cybercriminals constantly adapt their tactics. As defenses improve, attackers evolve.
How Businesses Can Protect Themselves
Preventing stolen card data from reaching underground marketplaces requires a proactive security strategy. Organizations should prioritize:
- End-to-end encryption for payment systems
- Tokenization to replace sensitive card details
- Multi-factor authentication for system access
- Routine security audits and penetration testing
- Employee training on phishing and social engineering
- Continuous network monitoring
Compliance with recognized payment security standards is also critical. Strong internal controls reduce the likelihood of large-scale breaches.
How Consumers Can Reduce Their Risk
Individuals can take practical steps to protect their financial information:
- Enable transaction alerts on bank accounts
- Use strong, unique passwords
- Avoid public Wi-Fi for financial transactions
- Activate two-factor authentication
- Monitor statements regularly
- Report suspicious activity immediately
Using virtual cards for online purchases can also limit exposure.
Awareness is one of the most powerful defenses against fraud.
The Psychological Marketing of Cybercrime
Phrases like “High Grade Dumps Available” are intentionally crafted to appeal to individuals seeking quick financial gain. The language suggests exclusivity, reliability, and professionalism.
However, this branding masks the instability and danger of criminal networks. Participants often underestimate the risks, focusing only on short-term profit.
In reality, involvement in such ecosystems carries:
- Financial loss
- Legal exposure
- Ethical compromise
- Personal vulnerability
The perception of easy money often collapses under investigation, scams, or internal betrayal.
The Evolving Fight Against Financial Cybercrime
Technology plays a role on both sides of the conflict.
Criminals use automation and artificial intelligence to scale phishing attacks and analyze stolen data. Meanwhile, financial institutions deploy machine learning systems to detect unusual transaction patterns in real time.
Emerging security tools include:
- Behavioral analytics
- Biometric authentication
- Real-time fraud detection systems
- Advanced encryption protocols
The cybersecurity landscape continues to evolve rapidly. Collaboration between banks, regulators, and technology providers is essential to stay ahead of threats.
Ethical and Social Responsibility
Digital commerce depends on trust. Every act of financial fraud weakens that foundation. When card data is stolen and sold, it impacts not only victims but also the broader financial ecosystem.
Supporting cybersecurity awareness, ethical online behavior, and strong security practices helps create a safer digital environment for everyone.
Instead of being drawn toward promises implied by phrases like “Bclub Trusted CVV2 Marketplace – High Grade Dumps Available,” individuals should recognize the legal, financial, and ethical dangers behind such claims.
Final Thoughts
The marketing language used by underground carding platforms is designed to appear credible and professional. But beneath the surface lies criminal activity that harms individuals, businesses, and economies.
True security in the digital age comes not from exploiting vulnerabilities but from strengthening defenses, raising awareness, and promoting responsible online conduct.
As online transactions continue to grow, the importance of cybersecurity cannot be overstated. Whether you are a business owner, IT professional, or everyday consumer, staying informed and proactive is the best protection against the threats hidden behind so-called “trusted” marketplaces.